In today’s cybersecurity landscape, managing privileged credentials securely is critical. One of the core components of CyberArk PAM is the Central Policy Manager (CPM), responsible for automating password lifecycle management.
This article provides a complete, practical guide on:
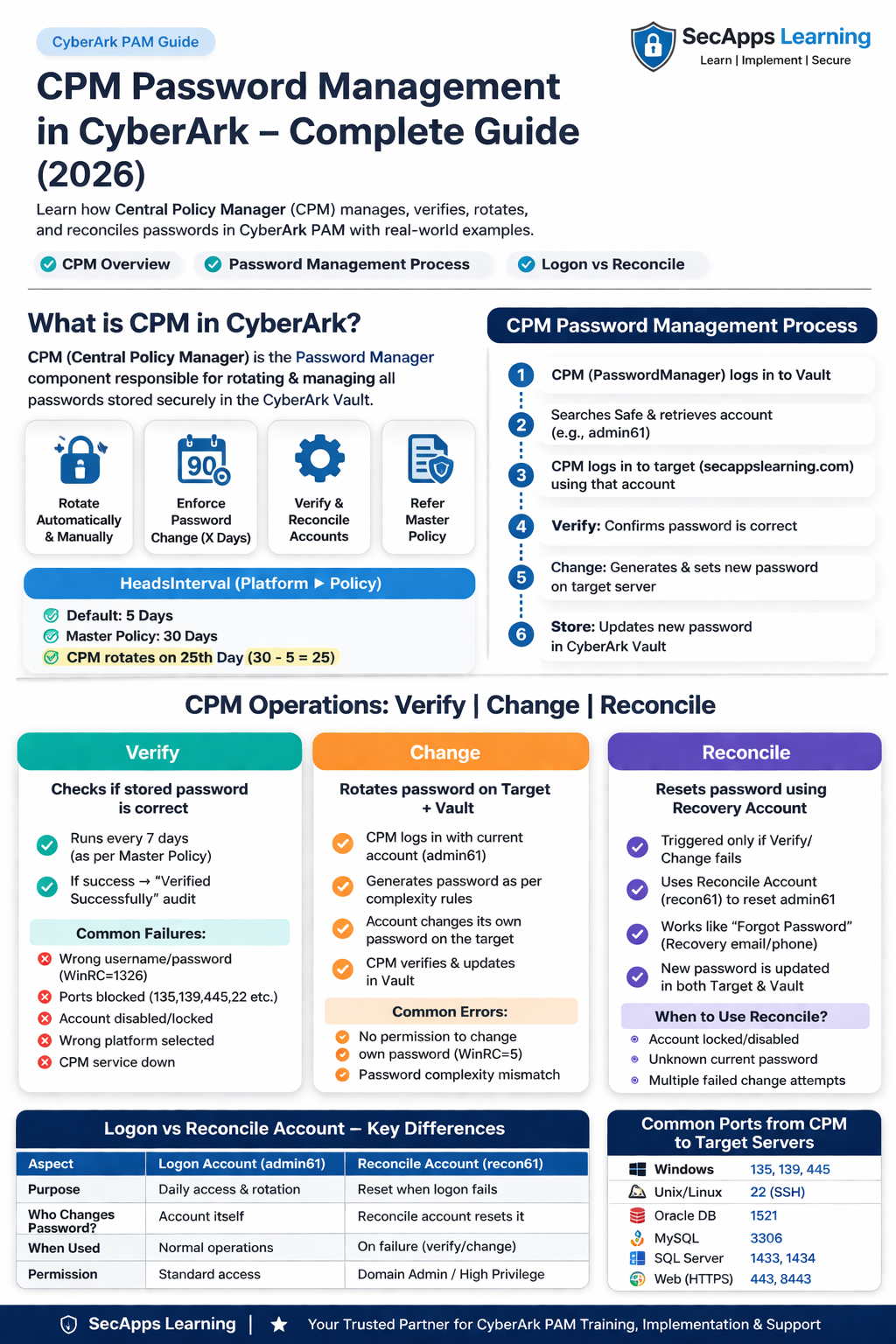
CPM Overview
Password Management Process (Verify, Change, Reconcile)
Difference between Logon (Change) and Reconcile Accounts
The Central Policy Manager (CPM)—also known as the Password Manager—is a CyberArk component responsible for:
✔ Automatic password rotation
✔ Manual password changes (on-demand)
✔ Password verification
✔ Enforcing password policies
CPM ensures that privileged account passwords are:
Changed regularly
Strong and compliant
Always synchronized between Vault and target systems
Password rotation is governed by:
Defines:
Password expiry duration (e.g., 30 days)
HeadStartIntervalDefines:
When CPM should rotate the password before expiry
Password Change in X Days = 30 days
HeadStartInterval = 5 days
👉 CPM rotates password on Day 25 (30 - 5)
When CPM is installed, it creates a default Vault account:
Used by CPM to authenticate into the Vault
Performs all password management operations
Verification ensures that the password stored in CyberArk matches the password on the target system.
Account: admin61
Address: secappslearning.com
Safe: Admin-Safe
CPM logs into Vault using PasswordManager
Searches for the Safe (Admin-Safe)
Retrieves account (admin61)
Uses stored credentials to log into target system
If login succeeds → ✅ Verified Successfully
| Issue | Cause | Resolution |
|---|---|---|
| WinRC=1326 | Invalid credentials | Verify username/password |
| Ports blocked | Network issue | Open required ports |
| Account locked/disabled | AD issue | Enable/unlock account |
| No login permission | Access issue | Grant required rights |
| Wrong platform | Misconfiguration | Correct platform |
| CPM service down | Infra issue | Restart CPM services |
| Wrong address | Typo | Fix DNS/hostname |
| GPO restriction | Policy block | Allow CPM access |
| No safe permission | Vault issue | Assign permissions |
| Account disabled in CyberArk | Disabled flag | Enable account |
Windows: 135, 139, 445
Unix/Linux: 22
SQL Server: 1433, 1434
Oracle: 1521
MySQL: 3306
Web: 443
In this phase, CPM updates the password both:
On the target system
In the CyberArk Vault
Verify login using current password
Generate new password (as per platform policy)
Change password on target system
Re-login with new password
Update password in Vault
| Issue | Cause | Resolution |
|---|---|---|
| All verify errors | Same as above | Fix accordingly |
| WinRC=5 | No password change rights | Grant permissions |
| Password complexity mismatch | Policy mismatch | Align target & CyberArk policy |
Reconcile is used when:
👉 CPM cannot verify or change password
A privileged recovery account used to reset passwords when the current password is unknown.
Managed Account: admin61
Reconcile Account: recon61
CPM logs into Vault using PasswordManager
Retrieves reconcile account (recon61)
Logs into target system using reconcile account
Resets password of admin61
Logs in using new password
Updates password in Vault
Just like clicking “Forgot Password” on a website and resetting via email or OTP.
| Feature | Logon Account (Change) | Reconcile Account |
|---|---|---|
| Usage | Regular password rotation | Password recovery |
| Dependency | Needs current password | Does NOT need current password |
| Account Used | Same account (admin61) |
Separate account (recon61) |
| Permission Required | Change own password | Reset other accounts |
| Trigger | Normal operation | Failure scenario |
✔ CPM automates password security lifecycle
✔ Verify ensures password accuracy
✔ Change rotates password securely
✔ Reconcile recovers access when password is unknown
✔ Proper configuration prevents 90% of issues
Mastering CPM Password Management is essential for:
CyberArk Engineers
PAM Administrators
Security Professionals
Understanding these processes not only helps in real-time troubleshooting but is also critical for CyberArk certifications like Defender and Sentry.
Your email address will not be published. Required fields are marked*
Copyright 2022 SecApps Learning. All Right Reserved
Comments ()