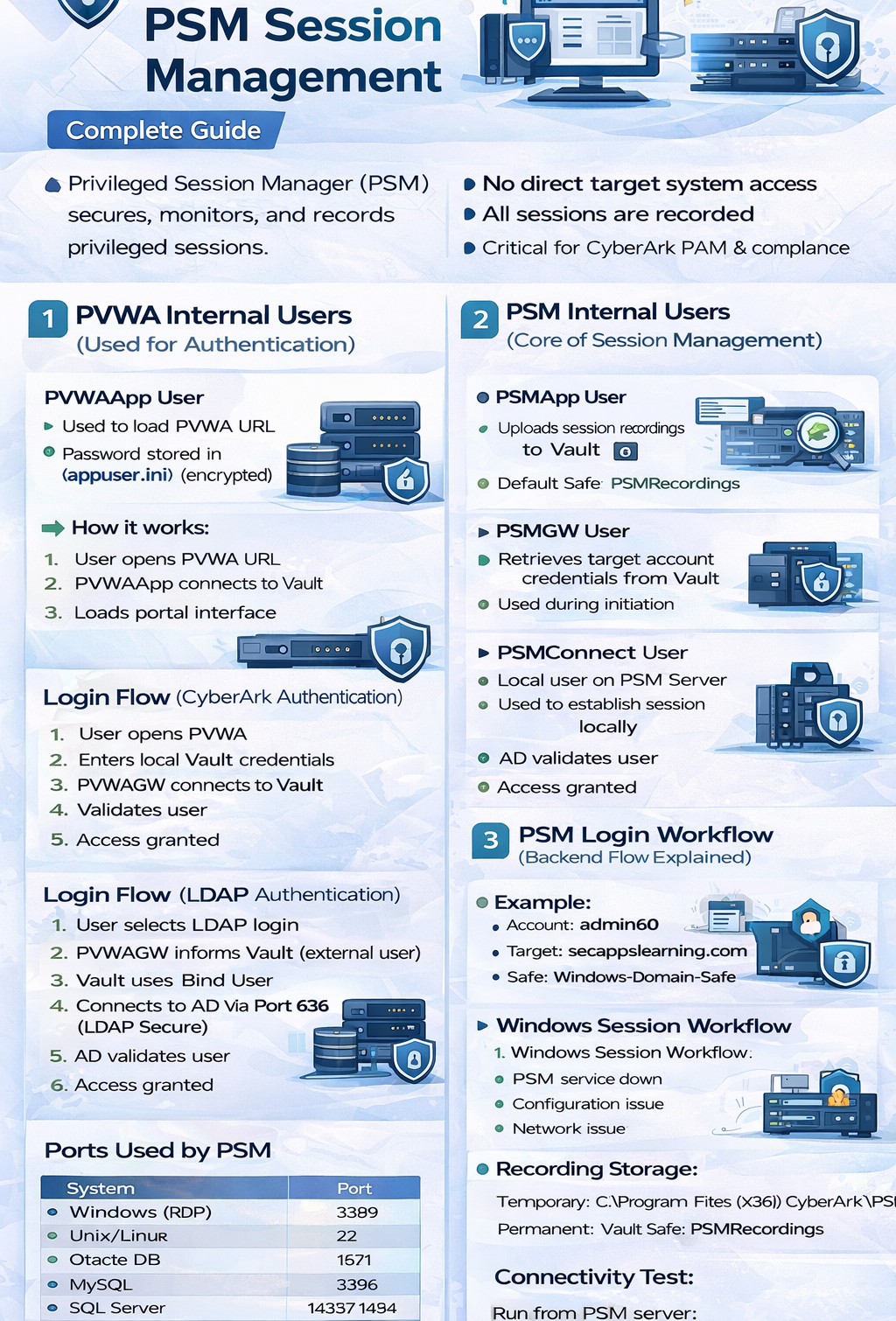
Learn CyberArk PSM Session Management in detail, including PVWA & PSM internal users, login workflow, session recording, and troubleshooting. Beginner to advanced guide.
CyberArk Privileged Session Manager (PSM) is a critical component used to secure, monitor, and record privileged sessions.
👉 It ensures that users never directly access target systems and all activities are:
Monitored
Recorded
Audited
CyberArk PVWA uses internal users to authenticate and authorize access.
Used to load PVWA URL
Password stored in:
👉 appuser.ini (encrypted)
User opens PVWA URL
PVWAApp connects to Vault
Loads portal interface
Used for user authentication & impersonation
Verifies user identity in Vault
User opens PVWA
Enters local Vault credentials
PVWAGW connects to Vault
Validates user
Access granted
User selects LDAP login
PVWAGW informs Vault (external user)
Vault uses Bind User
Connects to AD via Port 636 (LDAP Secure)
AD validates user
Access granted
Uploads session recordings to Vault
Default Safe: PSMRecordings
Retrieves target account credentials from Vault
Used during session initiation
Local user on PSM server
Used to establish session locally
Used for live session monitoring (shadowing)
Auditor role required
👉 Required group:
CyberArk_Auditors
Created for non-Windows connections
Example: Unix, DB, Network devices
Each user gets dedicated shadow user profile
Created automatically during connection
If user cannot connect:
👉 Possible cause: Corrupted shadow profile
Go to: lusrmgr.msc (PSM Server)
Delete shadow user
Reconnect → new profile created
Account: admin60
Target: secappslearning.com
Safe: Windows-Domain-Safe
PVWA redirects session to PSM
PVWAApp retrieves PSMConnect credentials
PSMConnect logs into PSM server
PSMGW retrieves target account password
Session established using admin60
User sees: “You’re being recorded”
After session ends → recording uploaded via PSMApp
Same flow with one change:
👉 Step 4:
Session established using PSMShadow user
Temporary:
C:\Program Files (x86)\CyberArk\PSM
Permanent:
👉 Vault Safe: PSMRecordings
| System | Port |
|---|---|
| Windows (RDP) | 3389 |
| Unix/Linux | 22 |
| Oracle DB | 1521 |
| MySQL | 3306 |
| SQL Server | 1433 / 1434 |
👉 Issue is with PSM Server
Possible causes:
PSM service down
Configuration issue
Network issue
👉 99% cases → Target server issue
Run from PSM server:
TNC TargetServerIP -Port <PortNumber>
✔ PSM ensures secure session access
✔ No direct login to target systems
✔ Sessions are always recorded
✔ Shadow users handle non-Windows connections
✔ Most issues are either PSM config or target system
Understanding PSM Session Management is critical for:
CyberArk Engineers
Security Administrators
Certification preparation (Defender/Sentry)
👉 Mastering PSM gives you strong control over session security, monitoring, and compliance.
Your email address will not be published. Required fields are marked*
Copyright 2022 SecApps Learning. All Right Reserved
Comments ()