Introduction to CyberArk Service Accounts
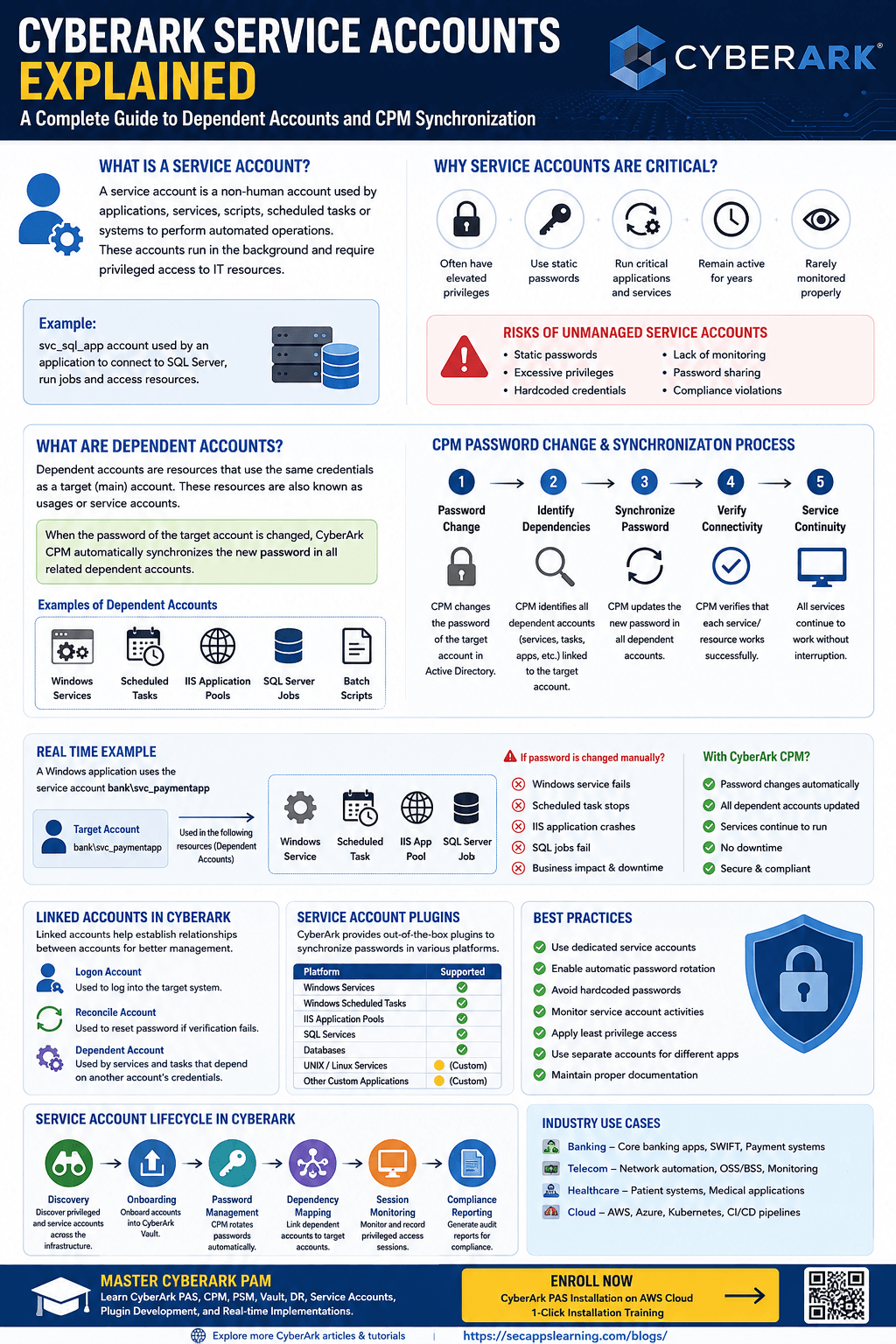
In modern enterprise environments, applications, services, databases, and automated tasks constantly communicate with each other without human interaction. These machine-to-machine communications require credentials to authenticate and access systems securely. These credentials are commonly known as Service Accounts.
Managing service accounts manually is one of the biggest security challenges in organizations because these accounts often:
🟦Have elevated privileges
🟦Use static passwords
🟦Run critical applications
🟦Remain active for years
🟦Are rarely monitored properly
This is where CyberArk Privileged Access Management (PAM) becomes extremely important.
CyberArk helps organizations securely manage, rotate, monitor, and synchronize service account passwords automatically without impacting business applications.
In this article, we will understand:
🟦What service accounts are
🟦What dependent accounts are
🟦How CyberArk manages service accounts
🟦CPM synchronization process
🟦Windows services and scheduled task examples
🟦Linked accounts in CyberArk
🟦Best practices for service account management
🟦Real-world enterprise scenarios
🟦Security risks of unmanaged service accounts
A Service Account is a non-human privileged account used by applications, services, scripts, scheduled tasks, databases, or systems to communicate with other systems automatically.
Unlike normal user accounts, service accounts are not used by humans for logging into systems interactively.
Instead, they are used by:
🟩Windows Services
🟩Scheduled Tasks
🟩Applications
🟩APIs
🟩Databases
🟩Middleware
🟩Backup tools
🟩Monitoring tools
🟩Automation scripts
These accounts usually run continuously in the background.
Imagine an organization using:
🟩SQL Server
🟩IIS Web Server
🟩Backup software
🟩Monitoring application
The IIS web application may need to connect to SQL Server automatically.
Instead of using a human administrator account, a dedicated service account is created such as:
svc_sql_app
This account:
🟩Starts the application service
🟩Connects to databases
🟩Runs background jobs
🟩Accesses shared resources
If the password changes manually without updating the application configuration, the service will stop working.
This creates operational and security challenges.
CyberArk solves this problem using CPM Password Management and Service Account Synchronization.
Service accounts are everywhere in enterprise infrastructure.
Large organizations may have:
🟩Thousands of Windows services
🟩Multiple scheduled tasks
🟩Application integrations
🟩Automation frameworks
🟩Cloud workloads
🟩Middleware servers
Many organizations lose track of these accounts because:
🟦Passwords never expire
🟦Teams fear outages
🟦Ownership is unclear
🟦Credentials are hardcoded
This creates huge security risks.
Many service accounts use the same password for years.
Service accounts often have administrator access.
Passwords may exist inside:
🟦Scripts
🟦Config files
🟦Applications
🟦Scheduled tasks
Most organizations do not monitor service account usage properly.
Multiple teams may know the same password.
CyberArk helps eliminate these risks using centralized privileged access management.
Learn more about PAM security concepts from SecApps Learning Blogs.
In CyberArk terminology, Dependent Accounts are accounts or resources that depend on another target account's credentials.
Dependent accounts are also called:
🟦Usages
🟦Service Accounts
🟦Password usages
These resources require the same password as the main target account.
When CyberArk changes the password of the main account, it automatically updates all linked dependent accounts.
This synchronization is performed by the Central Policy Manager (CPM).
Let us assume:
Main Target Account
Domain Account:
secappslearning\svc_app
This account password is used in:
🟦Windows Service
🟦IIS Application Pool
🟦Scheduled Task
🟦SQL Job
🟦Batch Script
All these become dependent accounts.
If CyberArk changes the password:
Old Password → New Password
CyberArk CPM automatically updates all connected services and tasks using the new password.
This ensures applications continue working without outages.
Scenario
A banking application runs on Windows Server.
The application uses a service account:
bank\svc_paymentapp
This account is configured in:
| Resource | Usage |
|---|---|
| Windows Service | Starts application |
| Scheduled Task | Runs nightly jobs |
| IIS App Pool | Web application access |
| SQL Server Job | Executes reports |
If the password changes manually:
🟩Windows service fails
🟩Scheduled task stops
🟩IIS application crashes
🟩SQL jobs fail
This creates production outages.
CyberArk CPM performs the following steps:
Step 1: Password Change
CPM changes the password in Active Directory.
Step 2: Identify Dependencies
CyberArk identifies all linked dependent accounts.
Step 3: Synchronize Password
CPM updates:
🟦Windows services
🟦Scheduled tasks
🟦Application pools
🟦Related configurations
Step 4: Verify Connectivity
CyberArk validates that the service works successfully.
This entire process is automated.
The Central Policy Manager (CPM) is responsible for:
Password rotation
Password verification
Password reconciliation
Service account synchronization
CPM ensures passwords are updated safely without impacting services.
Password Verification
CyberArk verifies the current password.
Password Rotation
The password changes automatically based on policy.
Dependency Discovery
CyberArk identifies dependent accounts linked to the target account.
Synchronization
The new password is updated everywhere.
Validation
CyberArk checks whether the service starts successfully.
A Windows Service often runs using a service account.
Example:
CyberArk Vault Service
SQL Server Service
Tomcat Service
IIS Service
Each service may use domain credentials.
Example
Service Name:
Apache Tomcat
Log On Account:
corp\svc_tomcat
If the password changes without synchronization:
🟩Tomcat service fails
🟩Application becomes unavailable
CyberArk prevents this issue.
Organizations heavily use Windows Scheduled Tasks for:
🟩Batch jobs
🟩Backups
🟩Reports
🟩Automation
🟩Scripts
These tasks run using service account credentials.
Example:
NightlyBackupTask
Runs as:
corp\svc_backup
CyberArk updates scheduled task credentials automatically during password rotation.
CyberArk supports Linked Accounts to establish relationships between accounts.
Linked accounts help manage:
Logon accounts
Reconcile accounts
Dependent accounts
Privileged escalation accounts
Logon Account
Used to log into a target system.
Reconcile Account
Used to reset passwords if verification fails.
Dependent Account
Used by services and tasks dependent on another account.
CyberArk provides several out-of-the-box plugins for service account management.
These plugins help CPM synchronize passwords automatically.
| Platform | Supported |
|---|---|
| Windows Services | Yes |
| Scheduled Tasks | Yes |
| IIS Application Pools | Yes |
| SQL Services | Yes |
| UNIX Services | Custom |
| Databases | Yes |
CyberArk also supports custom plugin development for unsupported platforms.
You can learn more about CPM plugin development from CyberArk technical blogs.
Managing service accounts is not only about password rotation.
CyberArk manages the complete lifecycle.
Discovery
CyberArk discovers privileged and service accounts across infrastructure.
Onboarding
Accounts are onboarded into CyberArk Safe.
Password Management
CPM automatically rotates passwords.
Dependency Mapping
Dependent accounts are linked to target accounts.
Session Monitoring
CyberArk monitors privileged access activities.
Compliance Reporting
Audit reports help organizations meet compliance requirements.
Banks use service accounts for:
SWIFT integrations
ATM systems
Payment gateways
Core banking applications
CyberArk helps secure these critical accounts.
Telecom organizations use service accounts for:
Network automation
Monitoring tools
OSS/BSS applications
Database integrations
Hospitals use service accounts for:
Patient management systems
Medical applications
Backup automation
CyberArk ensures compliance and security.
Cloud workloads use service accounts for:
AWS automation
Azure integrations
Kubernetes authentication
CI/CD pipelines
CyberArk secures cloud-native privileged identities.
Use Dedicated Service Accounts
Never use personal administrator accounts for services.
Always rotate passwords regularly using CyberArk CPM.
Use secure integrations instead of storing passwords in scripts.
Enable session monitoring and auditing.
Grant only required permissions.
Avoid sharing service accounts across applications.
Track:
Ownership
Dependencies
Criticality
Usage
Even with PAM solutions, organizations face challenges.
Older applications may not support automated password updates.
Applications may store passwords internally.
One account may be used across multiple servers.
Teams fear application outages during password changes.
CyberArk minimizes these risks through automated synchronization.
| Feature | User Account | Service Account |
|---|---|---|
| Used by Human | Yes | No |
| Interactive Login | Yes | Limited |
| Password Rotation | Manual | Automated |
| Used by Applications | No | Yes |
| Runs Background Tasks | No | Yes |
| PAM Requirement | Medium | High |
CyberArk modern interface allows administrators to:
Add dependent accounts
Manage usages
Link services
Configure synchronization
Monitor password updates
The interface simplifies service account management operations.
The classic interface also supports:
Dependent account configuration
Linked accounts
CPM usage management
However, most organizations now prefer the modern interface.
CyberArk is widely trusted because it provides:
Enterprise-grade PAM
Automated password rotation
Service continuity
Audit logging
Compliance support
Session monitoring
Dependency synchronization
It helps organizations reduce operational risks significantly.
Modern IT environments are moving toward:
Zero Trust Security
Identity-first security
Cloud-native PAM
Secrets Management
Machine Identity Protection
CyberArk continues expanding capabilities in:
Secrets management
DevOps security
Kubernetes security
Cloud PAM
Identity security
Service account management is becoming more critical than ever.
Service accounts are among the most critical yet overlooked privileged identities in enterprise environments.
Without proper management, they create major security risks such as:
Static passwords
Unauthorized access
Compliance violations
Service outages
CyberArk provides a powerful solution to securely manage service accounts and dependent accounts using:
Automated password rotation
CPM synchronization
Dependency management
Linked accounts
Secure privileged access
Organizations using CyberArk can ensure:
Better security
Reduced downtime
Compliance readiness
Operational efficiency
Understanding how dependent accounts and service accounts work is essential for every CyberArk engineer, administrator, and cybersecurity professional.
If you want to become an expert in CyberArk implementation, service account management, CPM plugins, and real-time PAM operations, practical training is extremely important.
Master CyberArk implementation, CPM, PSM, Vault, DR, Service Accounts, Plugin Development, Automation, and Real-Time Scenarios with hands-on practical training.
👉 Enroll Now – CyberArk PAS Installation on AWS Cloud 1-Click Installation Training
We will also connect you with advanced learning resources such as:
Your email address will not be published. Required fields are marked*
Copyright 2022 SecApps Learning. All Right Reserved
Comments ()