The cybersecurity industry is entering a major transformation phase where identity has become the new security perimeter. With the rapid adoption of Artificial Intelligence, cloud-native architectures, machine identities, and autonomous agents, enterprises are facing an exponential increase in identity complexity.
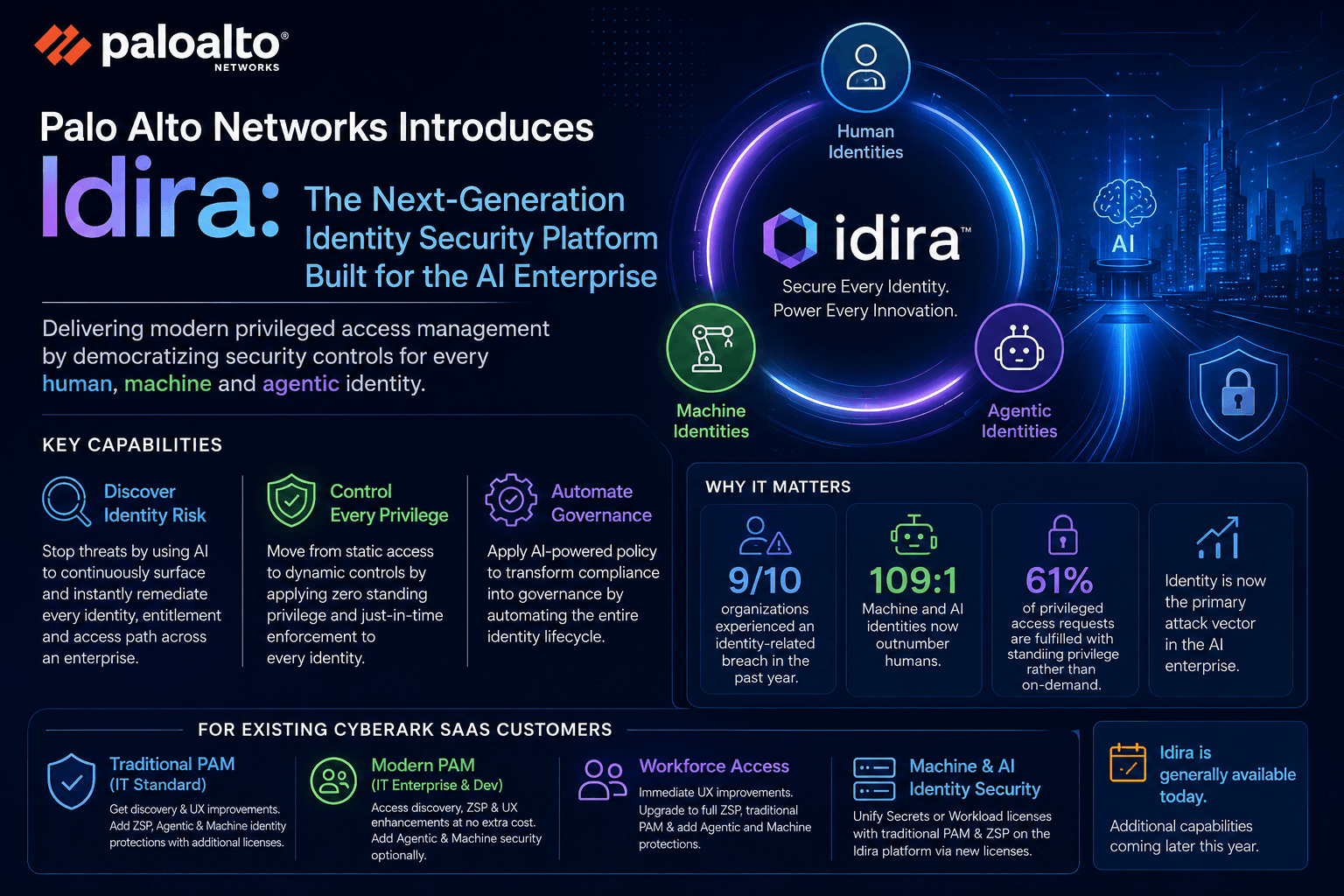
To address this shift, Palo Alto Networks has launched Idira, a next-generation identity security platform designed for the AI enterprise.
Idira expands identity security beyond traditional Privileged Access Management (PAM) by securing:
Human identities
Machine identities
AI agents
Workloads and applications
It introduces AI-driven governance, Zero Standing Privilege (ZSP), and dynamic access control as the new foundation of identity security.
This launch also modernizes capabilities for existing CyberArk customers while redefining how enterprises manage privileged access in the AI era.
Identity is now the primary attack surface in modern cybersecurity.
Attackers no longer rely only on network breaches. Instead, they exploit:
Credentials
API tokens
Service accounts
Machine identities
Privileged access pathways
Key industry observations highlighted during the Idira launch include:
9 out of 10 organizations experienced identity-related breaches
Machine and AI identities outnumber human identities by 109:1
61% of privileged access still relies on standing privileges
This shows that identity complexity has grown beyond what traditional security models can handle.
Idira is an AI-native identity security platform built by Palo Alto Networks to secure all identities across modern enterprises.
It goes beyond traditional PAM by unifying:
Identity discovery
Privilege control
Governance automation
Machine identity security
AI agent protection
Instead of static access management, Idira focuses on dynamic, intelligent, and risk-based identity security.
Traditional PAM solutions were built for a simpler IT environment where:
Privileged users were limited
Access was static
Infrastructure was on-premise
Identity sprawl was minimal
However, modern enterprises now operate across:
Multi-cloud environments
Kubernetes clusters
SaaS applications
DevOps pipelines
AI-driven systems
API-based architectures
In this environment:
Identities are dynamic
Machines outnumber humans
Access is temporary
AI systems operate autonomously
Traditional PAM tools cannot scale to this complexity.
Idira continuously discovers and maps all identities across the enterprise, including:
Human users
Service accounts
Machine identities
API keys
AI agents
Workloads
It identifies:
Excess privileges
Hidden access paths
Risky entitlements
Identity misconfigurations
One of the most important principles in Idira is Zero Standing Privilege.
Instead of permanent access:
No always-on admin rights
No persistent elevated permissions
Temporary access only when required
This significantly reduces attack surfaces.
Idira enforces Just-In-Time access:
Access is granted only when needed
Permissions are time-limited
Access is automatically revoked
Every request is validated dynamically
Machine identities include:
API keys
Tokens
Certificates
Service accounts
Workloads
Idira manages their full lifecycle:
Secret rotation
Access governance
Policy enforcement
Identity monitoring
AI agents now act autonomously inside enterprises.
They can:
Execute workflows
Access systems
Trigger automation
Interact with APIs
Idira introduces governance for AI agents through:
Behavioral monitoring
Identity lifecycle management
Dynamic privilege enforcement
Policy-based controls
Idira does not eliminate traditional PAM capabilities. Instead, it extends and modernizes them.
Existing PAM features such as:
Password vaulting
Privileged session management
Credential rotation
Safe-based access control
Account management workflows
still continue to exist.
The transformation is not replacement — it is redefinition of PAM’s role.
Earlier model:
PAM = Vault + privileged access control
Idira model:
Identity Security Platform = Core
PAM = One module inside it
Old model:
Permanent admin rights
Manual approvals
Static permissions
New model:
Zero Standing Privilege (ZSP)
Just-in-Time access
Context-based elevation
Old PAM:
Focused on storing credentials
Idira:
Focuses on discovering and securing all identities
Traditional PAM:
Focused on human administrators
Idira expands scope to:
Machines
APIs
AI agents
Workloads
Old model:
Periodic audits
Manual policy enforcement
New model:
Continuous monitoring
AI-driven decisions
Automated remediation
For existing CyberArk customers:
No disruption to current PAM systems
Gradual feature enhancement
Optional upgrade paths
Add-on modules for AI and machine identity security
Receive:
Discovery improvements
UX enhancements
Optional upgrades:
Zero Standing Privilege
Machine identity security
AI agent protection
Receive:
Immediate ZSP capabilities
Identity discovery enhancements
Improved access workflows
Receive:
Enhanced access experience
Upgrade to full PAM capabilities
AI identity protection options
Can unify:
Secrets management
Workload identity governance
PAM controls
ZSP enforcement
The traditional perimeter model no longer exists.
Modern enterprises operate in environments where:
Remote access is standard
Cloud infrastructure dominates
APIs connect everything
AI systems act autonomously
Attackers now target identity instead of infrastructure.
Common attack vectors include:
Stolen credentials
Overprivileged accounts
API token abuse
Misconfigured identities
Idira is designed specifically to secure this identity-first world.
AI is transforming enterprise operations.
AI systems now:
Generate code
Automate workflows
Access APIs
Manage infrastructure
Process sensitive data
These systems require identity and access control.
Idira introduces:
AI identity governance
Agent-based access control
Dynamic privilege enforcement
Continuous monitoring
If you want to deeply understand CyberArk architecture and enterprise deployments, explore:
👉 CyberArk Vault Deep Dive Guide
👉 CyberArk Privilege Cloud Complete Guide
👉 CyberArk vs BeyondTrust vs Delinea Comparison
PAM is evolving into AI-driven identity intelligence platforms.
Machine identities are now the fastest-growing identity category.
AI agents must be treated as governed identities.
Permanent access is being replaced by temporary access models.
Eliminates standing privileges and unnecessary access.
Automated governance simplifies audits.
Full identity mapping across enterprise systems.
Unified identity management reduces complexity.
Secure governance for AI-driven systems.
Enterprises may face challenges such as:
Legacy system integration
Identity sprawl complexity
Migration planning
Skills gap in AI security
Governance maturity
Successful adoption requires strong identity architecture and Zero Trust alignment.
The launch of Idira by Palo Alto Networks represents a major evolution in identity security.
It does not replace traditional PAM — instead, it transforms it into a broader AI-native identity security platform.
Core PAM capabilities still exist, but they now operate as part of a larger ecosystem that includes:
Human identities
Machine identities
AI agents
Cloud workloads
With capabilities like:
AI-driven discovery
Zero Standing Privilege
Just-In-Time access
Machine identity governance
Agentic identity protection
Idira sets a new benchmark for modern identity security.
For existing CyberArk customers, it provides a smooth evolution path into AI-driven identity security without disrupting current deployments.
The cybersecurity industry is clearly moving toward a future where every identity is continuously discovered, governed, and secured — in real time — across humans, machines, and AI systems.
Your email address will not be published. Required fields are marked*
Copyright 2022 SecApps Learning. All Right Reserved
Comments ()